Your message has been sent.
We’ll process your request and contact you back as soon as possible.
The form has been successfully submitted.
Please find further information in your mailbox.



If you’ve been around DeFi long enough, the CrossCurve exploit probably didn’t surprise you. On February 1, 2026, CrossCurve experienced a cross-chain incident that resulted in approximately $3M in losses. For us, this is not just “market news”. It’s a mandatory quality check before any partner integration. We are accountable both for our own architecture and for our clients’ safety. That’s why, in parallel with CrossCurve’s public updates, we reviewed the incident details and evaluated how the root cause could (or could not) impact our planned integrations.
So what exactly happened to CrossCurve? Without going unnecessarily deep into terminology, the issue was not a blockchain hack, but an unintuitive design pattern originating from the Axelar GMP SDK (v5.10.0) that can slip through even professional audits if the risk isn’t explicitly understood. The ReceiverAxelar contract itself had been audited and verified on-chain, yet the vulnerability sat deeper in an accelerated execution path for cross-chain messages, where a critical operation could be triggered without full source validation via the gateway. In CrossCurve’s specific case, the situation was further amplified by a weak confirmation threshold configuration (threshold = 1), which reduced the overall robustness of the validation model.
This incident is also a broader signal for Axelar integrators: by following official examples and inheriting from “express” execution contracts, projects can unintentionally expose a dangerous attack surface even if the rest of the code is correct and looks production-ready. Another important point is that the risk doesn’t disappear by itself when updating: even newer SDK versions contain similar patterns, and if teams migrate without recognizing the architectural issue, they may carry the risk forward. Practically, the takeaway is simple: any fast execution path must either be strictly restricted or reinforced with strong origin/authorization checks on the integrator side; otherwise, express-style mechanics can become a bypass of your own security assumptions.
At the same time, our stance on CrossCurve remains positive, and ironically, the complexity of their architecture makes this incident less of a universal, repeatable scenario than it might look at first glance. The exploit relied on a specific messenger/execution pattern (a particular SDK design choice), whereas the solution CrossCurve is now moving toward — and the one we are considering in our own products for secure cross-chain asset transfers — is not dependent on that vulnerable linkage. For that reason, even if we had already been integrated with CrossCurve at the time of the incident, this exact attack vector would not have impacted our architecture, because our trust and validation points are structured differently and do not rely on the same express execution path.
Finally, CrossCurve’s official update, published on February 13, 2026, effectively confirmed the conclusions our team reached independently. They are restoring the system in stages, starting with components that were not affected (the aggregator is already live, with routing via Rubic and Bungee), and then re-enabling the Token Bridge and Consensus Bridge with additional security measures. Notably, they stated the Consensus Bridge will only go live after completing enhanced security checks. This “restore only what is confidently verified, and harden before reactivation” approach aligns well with how we evaluate partner protocol maturity prior to integration.
That’s exactly why moving USDT from Tron into EVM networks isn’t as simple as plugging in a bridge and calling it a day. Tron is where a huge amount of USDT actually moves: fees were cheap (no more, hence the need for bridges), flows are familiar, and volumes are real. So when you say “we need Tron liquidity”, the real question is where the money sits, who’s allowed to move it, and what breaks when one assumption turns out to be wrong.
This article is here to slow that conversation down in a good way. I’ll walk you through the main ways USDT moves from Tron into EVM networks, how those approaches behave when real volume hits, and then step back to ask the only question that really matters: which risks are you actually willing to carry.
At this point, the question becomes how USDT actually moves from Tron into an EVM network, and what you’re assuming when you choose one path over another.
Most discussions get stuck at the protocol level, but this one won’t. Before naming specific solutions, I want to be explicit about the dimensions that actually matter once real volume is involved. In practice, every cross-chain design ends up making trade-offs along the same axes, even if the marketing language differs.
The first is liquidity. Some models require capital to be pre-positioned on both sides. Others avoid that entirely but introduce different forms of trust. The second is asset identity. Sometimes users receive what everyone agrees is “the” USDT. Sometimes they don’t, and that distinction has real downstream effects in DeFi. Then there’s cost behavior under load, finality speed, security assumptions, integration effort, and how dependent you become on someone else’s roadmap.
If you line these dimensions up, the design space collapses into four broad approaches. They’re not variations of the same thing because they solve different problems and fail in different ways. The table below is a quick orientation.
| Approach | Where liquidity lives | Asset type | UX at real volume | Primary risk |
| LP bridges / pools | Pre-funded on both sides | Native USDT | Good until pools drain | Liquidity exhaustion, imbalance |
| Lock-mint / burn-unlock | Locked on Tron | Bridged / wrapped | Predictable | Trust, fragmentation |
| Intent-based execution | With solvers / MMs | Depends on route | Very good if solvers stay | Solver exit, pricing |
| Hybrid entry | External liquid chains | Canonical-by-design | Stable if routing holds | Messaging, aggregation |
The important thing to note is that none of these approaches removes risk; they only redistribute it. Some concentrate risk in liquidity provisioning, while others push it into trust, execution logic, or external operators. Once that’s clear, the rest of the discussion becomes much simpler.
With this frame in mind, we can now walk through each approach in detail and look at what you actually get, and what you quietly take on, when you choose it.
The model is straightforward. A user deposits USDT into a pool on Tron and receives USDT from a corresponding pool on the target EVM chain. Ideally, no wrapped or synthetic tokens appear. The same asset moves across chains, but liquidity is required “here and there” to make that possible.
From the user’s point of view, this often feels close to a direct transfer. The bridge does not mint a new asset. It redistributes existing liquidity between pools deployed on different networks.
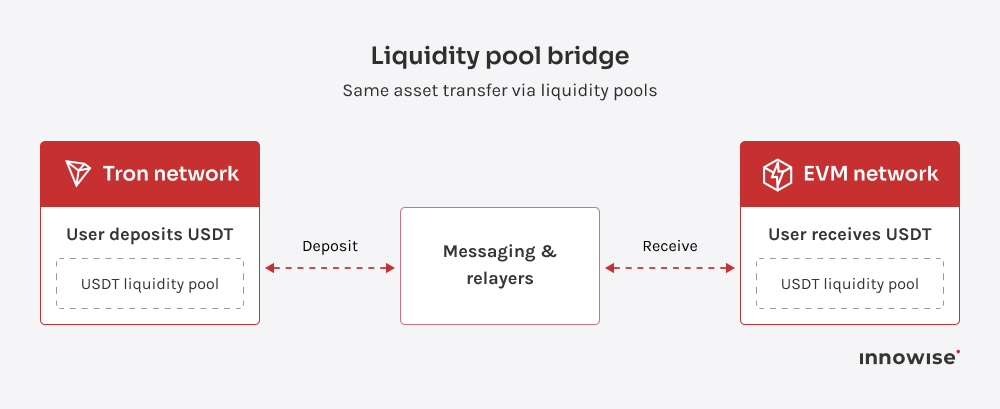
When LP bridges are set up correctly, they offer several clear advantages.
The main downside is liquidity. LP bridges require seed liquidity, sometimes in the millions. Without it, large transfers will “eat the pool”, leading either to hard limits or to a sharp increase in fees and slippage. This constraint applies regardless of which EVM network is on the receiving side.
There is also a critical dependency on messaging infrastructure. Bridges of this type rely on cross-chain messaging to coordinate pool releases, and most ready-made solutions integrate with major messaging providers. In practice, this means:
At that point, this is no longer “just connecting a bridge”. It is the launch and maintenance of a liquidity market.
LP bridges carry multiple layers of risk simultaneously.
Recent cross-chain incidents have shown how failures in message validation can cascade across networks. While those incidents did not necessarily involve LP pools, they underline that correct message handling sits on the critical path for pool-based bridges as well.
Allbridge Core (messaging inside Allbridge)
Allbridge is positioned as a cross-chain stablecoin swap built around the pool model, with fees distributed in favor of liquidity providers. Public materials emphasize that security does not rely on a single check, but on multiple practices and layers of control. Public communications also describe a fee split along the lines of “80% to LPs and 20% to the treasury”.
Stargate / LayerZero ecosystem (messaging via LayerZero)
Stargate historically addresses unified pools and imbalance dynamics by adjusting fees in response to flow direction. At the same time, the ecosystem has moved toward “official omnichain distribution” of stablecoins, including the emergence of USDT0 as an OFT asset under the LayerZero standard.
LayerZero documentation explicitly lists USDT0 as OFT-compatible. In public descriptions, the USDT0 launch follows a “lock on Ethereum, mint on target networks” model.
This is an important nuance. It shows that LP logic and lock-and-mint logic often blend in practice. In some cases, “nativeness” comes not from pools, but from issuer or infrastructure-level creation of a canonical omnichain asset.
Celer cBridge / Symbiosis State (messaging and validation via the Guardian Network)
These solutions typically offer broad chain coverage, but they return to the same underlying question: where does liquidity sit, and who holds it?
For EVM networks, the answer usually reduces to two options:
That recurring question of who funds the liquidity is what ultimately defines how far LP bridges can take an EVM ecosystem.
This model follows a different logic than liquidity pools. On Tron, the original asset is locked. On the destination side, a “bridged” version of that asset is minted. When funds move back, the bridged asset is burned, and the original asset is unlocked on Tron.
There are no pools that need to be balanced across chains. Capacity is determined by how much is locked, not by how much liquidity happens to be available elsewhere. However, there is a technical complexity to keep in mind. Because Tron and EVM-based networks differ significantly, most lock-and-mint bridges rely on different technologies on each side. This increases implementation complexity and raises the bar for correct operation, especially when stablecoins are involved.
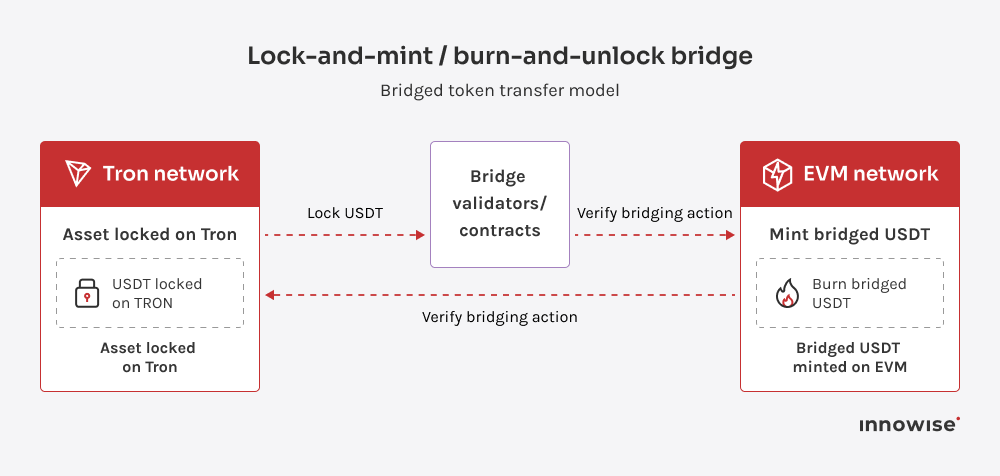
The trade-off is asset identity.
In almost all cases, a wrapped or bridged asset appears on the EVM network. This introduces several issues:
For stablecoins, this problem is especially acute. The market consistently prefers the most canonical version of an asset.
Lock-and-mint bridges remove the constant pressure of funding pools, but they replace it with questions of trust, asset identity, and long-term acceptance inside DeFi ecosystems.
Intent-based systems flip the usual flow on its head. Instead of telling the system how to move assets step by step, the user declares the outcome they want. For example, “I want USDT on the EVM network”. The routing, swapping, and bridging details are left to the market.
Solvers compete to fulfill that intent by offering quotes. Execution rules are enforced on-chain, so once a solver’s quote is accepted, settlement follows the protocol’s conditions. Atomicity comes not from a single bridge contract, but from the rules that govern how intents are matched and executed.
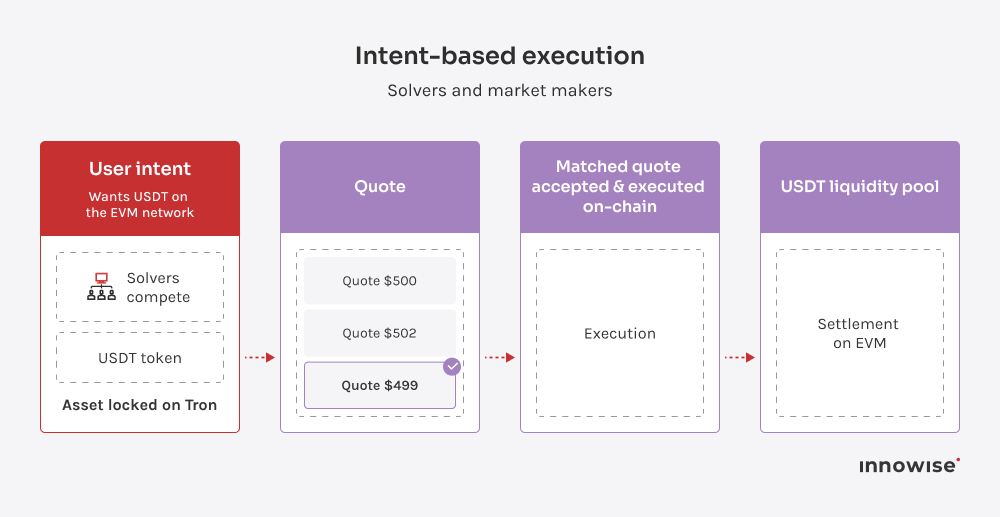
This model fits the Tron use case for a few concrete reasons:
When solver participation is healthy, intent-based execution delivers strong results.
The same properties that make intents attractive also define their limits.
Intent-based execution carries three main risks. There’s liveness risk if solvers leave. There’s price integrity risk if quotes become aggressive or distorted in low-liquidity conditions. And there’s operational risk, which means execution quality needs to be monitored and fallback routes must be available when intent execution degrades.
The hybrid model starts from a different premise than pool-based designs: don’t own liquidity.
Instead of trying to attract and maintain capital inside protocol-owned pools, the system relies on liquidity that already exists on large, liquid networks. The EVM network itself only controls the final entry and exit point, rather than the entire cross-chain route.
This design avoids the main constraint of LP-based bridges. There is no local pool to exhaust, because liquidity is not concentrated inside the destination network. There are no hard volume caps imposed by local TVL. Transfers scale with the depth of external markets, not the amount of capital the network managed to attract.
Liquidity stays where it already exists, on large chains, in established DEXs, and in mature routing systems.
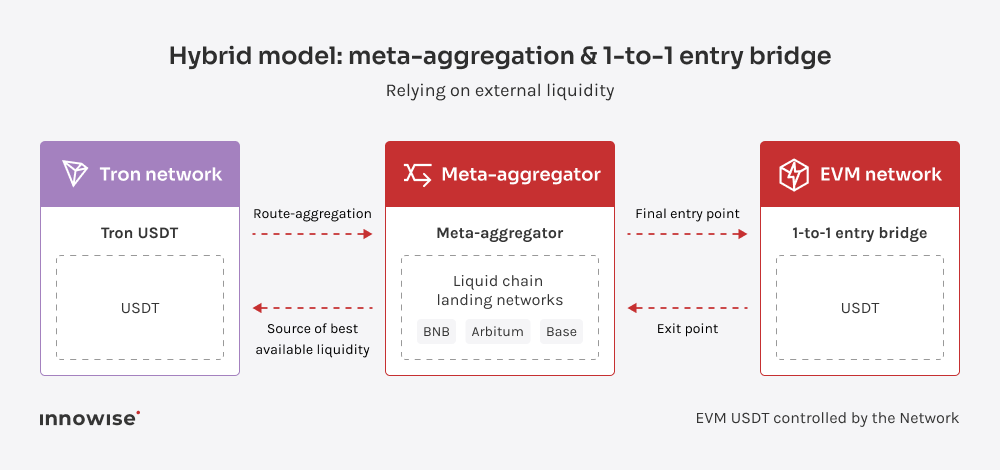
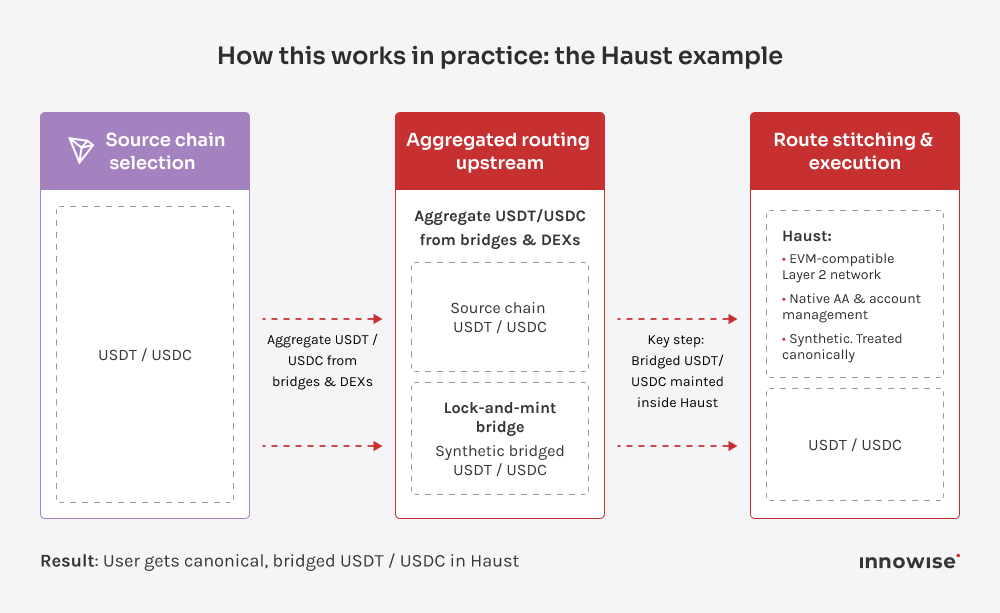
Haust is an EVM-compatible Layer-2 network built on zk-rollups, with native support for account abstraction, cross-chain execution, and aggregated routing. That makes it a good reference case for the hybrid model, because it already treats cross-chain entry as infrastructure, not an add-on.
In practice, the flow looks like this:
This asset is synthetic at the protocol level, but treated as canonical within Haust’s own DeFi stack.
The key property is that liquidity never sits inside Haust pools. It remains on large chains, DEXs, and aggregators. Haust controls execution correctness at the boundary and integrates the result directly into its wallet and account abstraction layer.
The hybrid approach does not come for free.
One trade-off is asset identity. A one-to-one bridge into the destination network creates a version of the stablecoin that is canonical within that network, but not globally. This requires a conscious decision about which assets are treated as canonical and which are considered imported or legacy.
There are also integration requirements. Messaging, indexing, and wallet support must be handled cleanly so the entry and exit experience feels coherent, even though the route spans multiple systems.
Finally, there can be timing constraints. Support for specific source chains, such as Tron, depends on aggregator and bridge roadmaps, which can introduce temporary delays.
It is important to understand that the hybrid model doesn’t shift risk, but eliminates it.
In exchange for giving up direct control over liquidity, the network gains flexibility and avoids becoming permanently dependent on its own balance sheet.
This incident wasn’t about a flashy “hack.” It was about one execution path that let a sensitive action run without the checks people assumed were there. My advice: use incidents like this the right way. Treat them as a forced audit of your assumptions. Write down what you trust, why you trust it, and what breaks if that trust is wrong.
If you want to go through your exact flow, step by step, and see where it can bend or snap, our blockchain consultants can review it with you before liquidity makes the decision for you.

Blockchain expert & DeFi analyst
Andrew lives and breathes blockchain. He helps clients navigate a space that’s constantly evolving — translating big ideas into technical strategies that are secure, scalable, and built for real-world use.









Your message has been sent.
We’ll process your request and contact you back as soon as possible.

By signing up you agree to our Privacy Policy, including the use of cookies and transfer of your personal information.