Your message has been sent.
We’ll process your request and contact you back as soon as possible.
The form has been successfully submitted.
Please find further information in your mailbox.



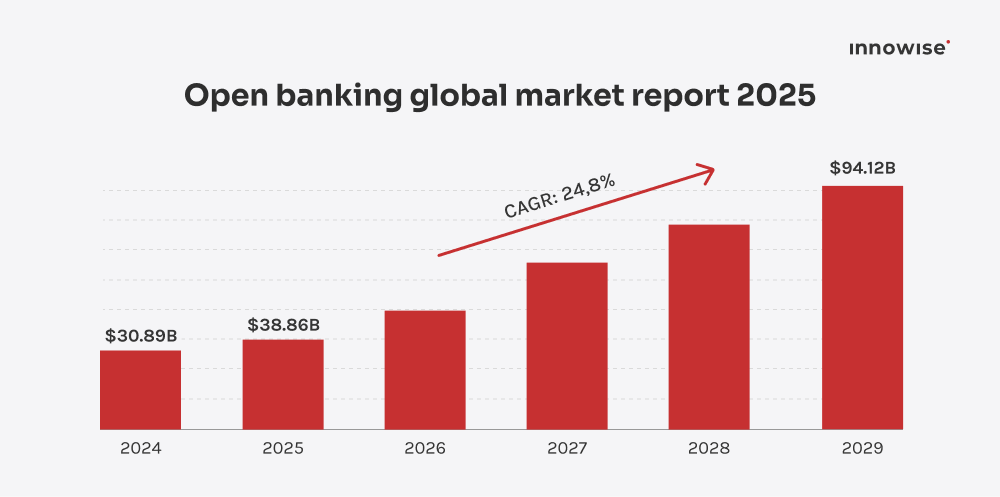
Global open banking services are now used by more than 470 million people worldwide, and API-based access to bank data underpins everyday functions like onboarding, payments, reconciliation, and credit decisions. At that level, bank APIs stop being “integrations” and start behaving like core infrastructure. Early structural choices often fade into the background until growth or regulation makes them hard to change.
In this guide, I focus on those execution choices. Not what bank APIs are, and not why they exist, but how teams structure them in practice, where problems usually appear, and what to think through before those problems are locked in. The goal is to help you assess bank API integration as an operating model, rather than just a technical task.
Bank API integration is often described as a technical link between a product and a bank. That’s accurate, but incomplete. In practice, it sets the boundaries for how a financial product operates. It affects how data moves, how decisions are made, and how much manual work sits behind the scenes once the product is live.
Well-structured integrations shape how the business functions across several areas:
Business model
Speed to market
Customer experience
Bank API integration exists within a very different banking environment than it did a decade ago. Open banking initiatives have encouraged banks to make customer-approved data available through APIs. In Europe, this took shape through PSD2. In the UK, through a dedicated open banking framework. In the US, data sharing has evolved through market-led agreements rather than a single regulatory mandate.
What these approaches have in common is a shift away from closed banking systems. Financial products no longer operate in isolation. Data moves between banks, fintechs, and third parties based on customer consent, supporting use cases like account aggregation, payment initiation, and real-time financial insights.
This ecosystem-based setup is what makes bank API integration strategically important. It allows products to participate in broader financial workflows rather than replicating functionality internally. For businesses, that means faster access to bank data, clearer paths to partnerships, and more flexibility in how financial services are delivered across platforms.
Structuring bank API integration well doesn’t change what a product offers. It changes how reliably the organization can operate as usage grows and more teams and partners depend on the same connections.
Internally, this usually shows up as:
Externally, this tends to result in:
For executives, the real question is rarely what bank API integration is. It’s whether now is the right moment. Timing matters because integrating too early creates drag, while waiting too long can lock teams into manual workarounds that are hard to unwind.
The answer depends less on company size and more on operating reality.
For early teams, bank API integration can be useful, but it’s rarely urgent.
Integration often makes sense when:
Integration is often premature when:
At this stage, committing to full integration too early can pull focus away from product fit.
This is where bank API integration usually becomes unavoidable.
Integration is often necessary when:
Delaying integration at this stage often creates risk:
For many scale-ups, this is the point where integration stops being optional and starts affecting growth and cost control.
For incumbents, the question isn’t whether bank APIs are needed, but how broadly they should be used.
Integration is often driven by:
Delaying structured integration here can lead to:
At this stage, the challenge is less about building APIs and more about deciding where they sit in the organization.
The decision to integrate bank APIs rarely comes down to a single trigger. It’s usually a choice between staying with the current setup or taking on the cost and commitment of integration. A useful way to frame the decision is this: if the current approach is influencing product scope, delivery speed, or compliance posture more than the integration itself would, it’s time to move forward.
Not all bank APIs serve the same purpose. Teams often group them together, but in practice, they solve different problems, come with different obligations, and introduce different trade-offs. Understanding these differences early helps avoid mismatched expectations later.
Open banking APIs provide secure, customer-approved access to bank data for third parties. Their scope and behavior are usually shaped by regulation.
They typically involve three parties:
Open banking APIs are commonly used for account aggregation, financial insights, and payment initiation, where regulatory frameworks apply.
Bank data APIs focus on retrieving financial information, whether through open banking frameworks or proprietary agreements.
Common data includes:
These APIs are often the foundation for reporting, analytics, lending decisions, and cash-flow visibility. Their usefulness depends heavily on data freshness, consistency across banks, and update frequency.
Payment APIs allow systems to initiate and manage money movement directly.
Typical use cases include:
Compared to read-only data APIs, payment APIs carry a higher operational and regulatory weight because they involve direct movement of funds.
Beyond data access and payments, many financial products rely on additional API categories that sit alongside core bank integrations:
These APIs are often combined with bank data APIs rather than used on their own.
Comparison of common bank API types
| API type | Primary business use cases | Data sensitivity | Regulatory requirements | Implementation complexity |
| Open banking APIs | Account aggregation, payment initiation, and financial insights | High | Defined by region (e.g. PSD2, UK Open Banking) | Medium to high |
| Bank data APIs | Reporting, analytics, and lending decisions | Medium to high | Varies by access model | Medium |
| Payment APIs | Transfers, payouts, and real-time payments | Very high | Strong oversight and controls | High |
| KYC/AML APIs | Identity checks, compliance screening | High | Strict, jurisdiction-specific | Medium |
| Fraud detection APIs | Risk assessment, transaction monitoring | Medium | Indirect, often policy-driven | Medium |
| Loan and credit APIs | Credit servicing, exposure tracking | High | Lending and data regulations | Medium to high |
Each API type brings different responsibilities and constraints. Many products use several of them at once, but not all need the same level of depth or control in every category.
From here, the next practical question is how to access these APIs. Whether to build direct connections, rely on intermediaries, or combine both approaches. That’s what the next section covers.
Once the decision to integrate bank APIs is made, attention shifts to the integration model. Most teams choose between direct bank connections, API aggregators, or a mix of the two. The right option depends on priorities, internal capacity, and the level of control the business needs to keep over data and operations.
This approach means connecting directly to individual banks and managing those connections in-house.
What this looks like in practice
When teams choose this
Trade-offs to consider
Aggregators sit between your product and multiple banks, offering a single access layer.
What this looks like in practice
When teams choose this
Trade-offs to consider
Many mature products combine both models.
What this looks like in practice
When teams choose this
Trade-offs to consider
Bank API integration models compared
| Factor | Direct integrations | Aggregators | Hybrid |
| Time to market | Slower at the start | Faster at the start | Fast for broad coverage, slower for selected banks |
| Cost over time | Higher upfront, lower per unit | Lower upfront, ongoing fees | Aggregator fees for most banks, direct costs for key ones |
| Regulatory exposure | Mostly internal | Shared with the provider | Split by integration type |
| Vendor dependence | Low | Higher | Depends on which banks use aggregators |
| Ability to grow coverage | Slower, bank by bank | Faster across regions | Broad coverage via aggregators, deeper control where needed |
A practical way to decide between models is to separate short-term needs from long-term constraints.
If speed and coverage matter most right now, aggregators often make sense. If control, data behavior, or cost predictability matter more over time, direct integrations become attractive. Hybrid setups usually appear once products have enough volume to justify different approaches for different banks.
This choice doesn’t need to be permanent. But it does need to be intentional, because switching models later is rarely trivial.
In the next section, we’ll look at how to choose the right bank API provider, regardless of which model you start with.
In practice, choosing a bank API provider happens in two steps. First, teams rule out options that don’t fit their operating reality at all. Only then does it make sense to compare the remaining providers side by side.
These checks answer a simple question: could this provider reasonably work for us? If the answer is no, there’s little value in going further.
Key areas to check include:
If a provider raises concerns in any of these areas, those concerns tend to resurface later as operating work rather than one-time setup issues.
Once a provider passes the baseline checks, the decision becomes comparative. At this stage, the goal is to understand trade-offs and decide which gaps are acceptable.
Common comparison areas include:
Different businesses will weigh these areas differently. What matters is being explicit about those priorities before a provider is selected.
The biggest mistake is treating bank APIs like a vendor purchase. The real test comes months later, when volumes rise, audits start, and a bank changes something without warning. The best provider on paper isn’t always the easiest to run in production. Be picky here. Ask uncomfortable questions, push for clear answers, and don’t hesitate to walk away if something feels vague.

Delivery Manager in fintech
Once a provider and integration approach are chosen, the work becomes operational. At this stage, success depends less on architecture diagrams and more on how clearly decisions are made before the first connection goes live.

Define exactly how bank data or payments will be used. Common cases include account aggregation, payment initiation, fraud checks, and financial analytics. Clear use cases help avoid building unnecessary integrations.

Decide whether to use aggregators, direct bank integrations, or both. Aggregators suit broad coverage and faster starts. Direct integrations suit specific banks, higher volume, or tighter control over data and behavior.

Set the basic structure before coding. Decide on API styles (REST or SOAP), where integrations run, how credentials are managed, and which internal systems depend on bank data.

Build against sandboxes, but test for real conditions. Validate data, test authentication and permissions, and check failure cases. Expect production behavior to differ from test environments.

Once live, focus on operation. Track performance, errors, and consent status. Assign clear ownership for monitoring and response so issues don’t linger or get passed between teams.

Define exactly how bank data or payments will be used. Common cases include account aggregation, payment initiation, fraud checks, and financial analytics. Clear use cases help avoid building unnecessary integrations.

Decide whether to use aggregators, direct bank integrations, or both. Aggregators suit broad coverage and faster starts. Direct integrations suit specific banks, higher volume, or tighter control over data and behavior.

Set the basic structure before coding. Decide on API styles (REST or SOAP), where integrations run, how credentials are managed, and which internal systems depend on bank data.

Build against sandboxes, but test for real conditions. Validate data, test authentication and permissions, and check failure cases. Expect production behavior to differ from test environments.

Once live, focus on operation. Track performance, errors, and consent status. Assign clear ownership for monitoring and response so issues don’t linger or get passed between teams.
Security and compliance around bank API integration don’t appear all at once. They surface at different points in the lifecycle of an integration, from early design decisions to day-to-day operation and formal reviews. Thinking about them in that order helps you focus on the right concerns at the right time.
Most security and compliance foundations are set before the first request is sent to a live bank API. Decisions made here tend to stay in place longer than expected.
At this stage, it is important to focus on:
This is also the point where you should agree internally on how bank data will be stored, who can access it, and which systems are allowed to consume it. Getting these basics clear early reduces friction later.
After go-live, security and compliance move from design to operation. Bank data starts flowing through real user journeys, and expectations around reliability and traceability increase.
At this stage, you should pay attention to:
This is where the shared responsibility model becomes visible in practice:
Being explicit about this split makes daily operation calmer and response to issues more direct.
The third phase is often triggered by an external event, such as a regulatory review, a customer complaint, or a service disruption.
When this happens, you are usually expected to demonstrate:
This is where regional frameworks come into play:
Planning for this phase upfront usually makes audits and incidents less disruptive.
By this point, it’s clear what bank APIs are and how they’re integrated. What tends to be less obvious is how the same building blocks are used very differently depending on the business model. Here’s how that usually looks in practice.
For fintechs, bank APIs are part of the decision engine. They’re rarely used once and discarded.
A typical setup pulls account and transaction data on a schedule, normalizes it, and feeds it into services that handle onboarding checks, credit limits, pricing, or monitoring. As new transactions arrive, decisions update automatically.
Where fintechs get value is in reuse. The same bank data supports onboarding, ongoing reviews, and alerts. Where they get burned is inconsistency. Different banks report balances, pending items, and timestamps differently. Teams that don’t centralize handling early usually end up with overrides and manual reviews later.
Banks use APIs mainly to control access. Externally, APIs define what partners can see and do without exposing core systems. Internally, the same APIs reduce point-to-point links between teams.
In practice, this means partner onboarding becomes more predictable, access rules live in one place, and audit trails are easier to follow. Banks that skip this layer often find that each new partner adds permanent operational overhead.
Here, bank APIs are tied to money flow rather than insight. They sit between orders, delivery events, and payouts.
Platforms use them to initiate payments, wait for confirmation, release funds, and reconcile transactions back to internal records. The hard part isn’t sending money. It’s handling late updates, retries, and partial failures without human involvement. When this is done well, finance teams stop chasing edge cases and start trusting the system.
Today, bank API integration is under pressure from higher expectations around security, payment timing, and data quality. In 2026, the focus shifts from adding endpoints to making existing connections predictable and easier to operate. Here are the trends I’d advise you to plan around.
Banks and providers are moving away from “our special OAuth setup” and toward common security profiles. The OpenID Foundation finalized key parts of FAPI 2.0 in 2025, including the Security Profile and Attacker Model, and later Message Signing. In 2026, that matters because more partners will expect these kinds of controls as the baseline for sensitive financial APIs.
In the euro area, instant payment rules hit major milestones in 2025, including sending instant payments and verification of payee tied to October 9, 2025. That’s now in the rear-view mirror. In 2026, “it settles in seconds” is becoming the normal expectation for many euro payment flows, which puts pressure on how you track payment status and handle exceptions.
SWIFT confirmed that the ISO 20022 coexistence period for cross-border payment instructions ended on November 22, 2025. So more structured fields are now flowing through payment messages. If your internal systems flatten that into free text, you lose the benefit and reconciliation stays painful.
The useful ML work around bank APIs is narrow. Think anomaly detection in payment flows and transaction monitoring. The BIS has published research on machine-learning methods for spotting anomalies in payment systems and on analytics for real-time retail payment monitoring. In 2026, the takeaway is simple: these tools only work if your bank data is consistent and refreshed often enough.
The realistic use is mostly on the “wholesale” side. Tokenised settlement experiments, cross-border rails, shared state between institutions. BIS Innovation Hub works like Project Agorá and ECB material on tokenisation point in that direction. If you’re not in institutional payments or markets, keep this as a watch item, not a roadmap item.
By the time teams start thinking seriously about bank API integration, the question is rarely whether to connect to banks. That decision is already made. The harder part is deciding how those connections should be structured, who owns what, and how much flexibility the setup needs to support growth, regulation, and partnerships over time.
That’s where bank API setup becomes a strategic concern. Teams planning a new integration, entering additional markets, or revisiting an existing setup often reach a point where internal assumptions need a second look. Questions around structure, ownership, and long-term impact are easier to address before they are embedded in production systems. Innowise works with organizations at that stage to help assess options and clarify trade-offs early.
A short, focused consultation can be enough to confirm whether the current approach holds up or where adjustments may be needed for what comes next.

FinTech Expert
Siarhei leads our FinTech direction with deep industry knowledge and a clear view of where digital finance is heading. He helps clients navigate complex regulations and technical choices, shaping solutions that are not just secure — but built for growth.











Your message has been sent.
We’ll process your request and contact you back as soon as possible.

By signing up you agree to our Privacy Policy, including the use of cookies and transfer of your personal information.