- Core system development
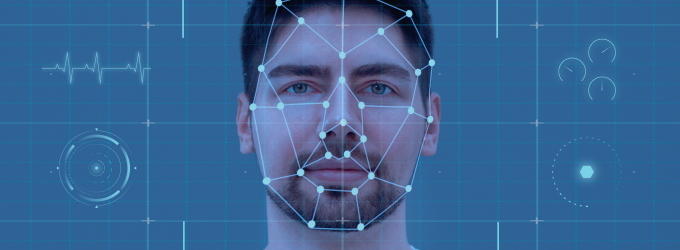
- Face detection and tracking
- Face identification systems
- Face authentication solutions
- Facial emotion recognition
- AI-driven face analytics
- Algorithm integration into existing systems
- Facial recognition system migration
- Multi-factor authentication integration
- Database architecture and management
- Privacy-first system design
Core system development
We architect end-to-end processing pipelines on highly available AWS infrastructure that combines liveness detection and 3D depth-mapping technology, so that enterprises can guarantee rock-solid security against fraud.
Face detection and tracking
Our software uses detection models in real time to locate faces in low-resolution CCTV video feeds, combined with re-identification (Re-ID) algorithms that track individuals across multiple camera zones.
Face identification systems
We create 1:N identification systems utilizing ArcFace embeddings in order to match faces against databases of millions of records, tuned for high throughput and a false acceptance rate below 0.01%.
Face authentication solutions
Our experts build secure 1:1 biometric authentication systems with passive liveness detection that excludes any form of printed photos, 3D masks, and deepfake replays, delivering passwordless access control for enterprise environments.
Facial emotion recognition
We implement emotion analysis using visual transformers to detect facial expressions in real time, so you can access data about your customers' behavior, track the sentiment of your retail store, and determine the level of engagement.
AI-driven face analytics
Our specialists design batch-processing analytics modules with real-time dashboards for decision-makers that scan video archives for behavioral patterns, anomaly flags, and attendance trends.
Algorithm integration into existing systems
We incorporate highly optimized PyTorch and ONNX deep learning models into existing legacy surveillance setups and enterprise software with full performance validation after deployment.
Facial recognition system migration
We modernize old-hat biometric infrastructures by directly moving old data into secure, cloud-based AI pipelines on AWS EKS, while also preserving historical identity data and full operational continuity.
Multi-factor authentication integration
We combine facial biometrics with one-time-password (OTP) codes, smart cards, and behavioral biometrics to build layered identity verification pipelines that meet zero-trust security requirements across enterprise environments.
Database architecture and management
Our data experts design and optimize high-throughput vector databases for facial embedding storage, with AES-256 encryption, indexed nearest-neighbor search, and auto-scaling for millions of identity records.
Privacy-first system design
We implement a match-on-device architecture, AES-256 data encryption, consent management APIs, irreversible facial hashing, and anonymization pipelines to make sure that biometric systems are compliant with all of the privacy requirements of GDPR, HIPAA, and CCPA.