Your message has been sent.
We’ll process your request and contact you back as soon as possible.
The form has been successfully submitted.
Please find further information in your mailbox.



So you want to build a trading app. Not a demo. Not a “we can place a fake order in a sandbox” prototype. A real platform that people trust with real money, that can survive market spikes, regulator questions, and the kind of user growth that breaks weaker systems.
If you’re nodding, you’re in the right place.
This guide walks through what stock trading app development really involves. Compliance basics, must-have features, tech stack options, and a practical way to pick a development partner without gambling on vibes.
Let’s not pretend “a stock trading app” is a singular product. Before you choose a stack or sketch screens, answer this: Are you building a brokerage, or are you building an investing front end that sits on top of someone else’s brokerage rails?
That single decision changes everything: licensing, compliance scope, architecture, timelines, and cost.
Here are the common routes.
You control order routing, clearing relationships, customer agreements, and books and records. You also inherit a host of regulatory duties, including record retention rules. For example, FINRA points firms to SEC Exchange Act Rule 17a-4 requirements for electronic recordkeeping formats.
You focus on onboarding, UX, education, funding, portfolios, and a clean trading flow. The brokerage partner handles parts of execution and custody, but you still have obligations around privacy, security, disclosures, and operational resilience. If you’re in the UK, the FCA has explicit expectations around outsourcing and operational resilience.
This is where a lot of “all-in-one” apps land. For example, in the latest project I participated in, the goal was an all-in-one mobile app for novice investors, including account opening, funding, trading, FX, analytics, and document flows like W-8 and FATCA/CRS inside the app.
If you’re not sure which bucket you’re in, here’s a quick heuristic:
Now let’s talk compliance, because it drives product design far earlier than most teams expect.
Nobody likes to hear this, but it’s true: compliance is not a checklist you paste in during QA. It shapes your data model, audit logs, user flows, and vendor choices. Below are the common areas that hit stock trading apps.
If you’re in the US broker-dealer world, recordkeeping expectations are not “nice to have.” FINRA Rule 4511 requires firms to make and preserve books and records, and it points to SEC requirements like Rule 17a-4 for format and retention details.
What this means in product terms:
If you’re operating under MiFID II in the EU, best execution is a core obligation. ESMA’s materials reference Article 27 requirements around describing processes and implementing order execution policies.
In product and platform terms, that pushes you toward:
If you operate in the EU, the Digital Operational Resilience Act (DORA) applies from 17 January 2025 and is aimed at strengthening ICT risk management for financial entities, including incident reporting expectations.
In the UK, FCA guidance on outsourcing and operational resilience is explicit about what it expects from firms using third parties.
Translation into engineering work:
If you touch personal data for EU users, GDPR Article 32 is the part that gets referenced constantly. It requires “appropriate technical and organisational measures” based on risk, including things like encryption where appropriate.
And if you accept card payments for funding, PCI DSS becomes part of your world, because it defines security requirements for environments handling payment account data.
Trading apps are a juicy target. So you need a benchmark that security teams can actually test against. OWASP MASVS is widely used as a mobile app security verification standard.
If you want a practical way to use MASVS, treat it as a set of acceptance criteria for mobile hardening, storage, auth, and network security testing.
Major regulations and security standards that shape stock trading apps
Let’s do this in two layers: user-facing features, then “quiet features” that keep your compliance and ops teams sane.
Most serious apps land on a core set:
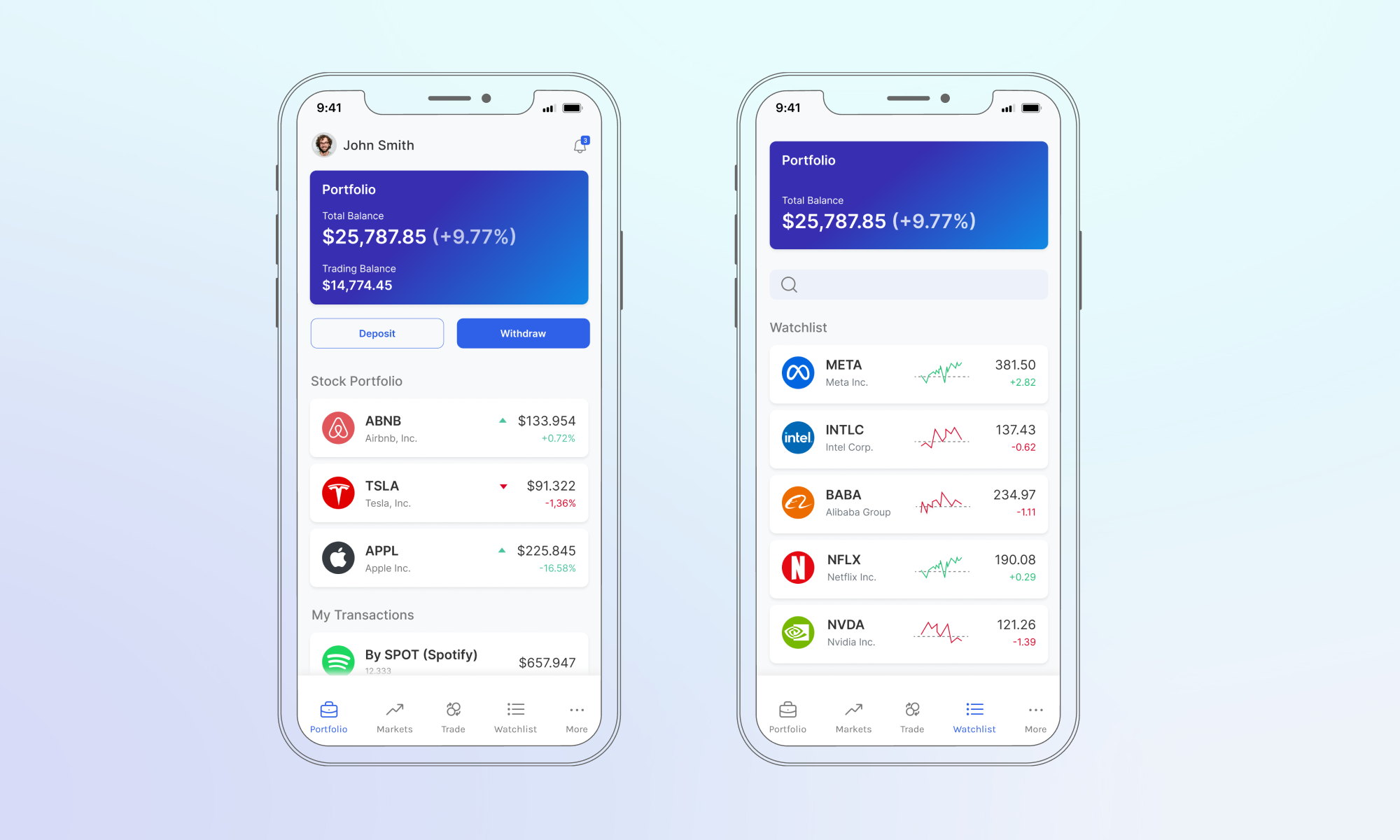
These are rarely flashy, but they’re the difference between “we launched” and “we can operate.”
Want a quick gut-check question? Ask your team this: If a regulator asks, “Show me exactly what happened to this user’s order at 10:03:11,” can you answer within minutes?
If not, you have design work to do.
“Stock trading app development works best when you design for audits, failure, and peak traffic from day one. Build clear event logs, strict access controls, and tested recovery paths before adding extra features. That is how you protect users, reduce support load, and keep regulators calm.”

Chief Delivery Officer & Head of Competence Center
Now we’re getting into the part that decides whether you sleep at night. A trading app isn’t just “mobile + API + database.” It’s a distributed system tied to third parties, market volatility, and strict correctness requirements.
Here are the architecture topics that show up in almost every serious build.
Orders and transfers are naturally event-based. Each step produces an event you must log, replay, and reconcile. This is why many teams move toward message queues and event logs early, especially when integrating multiple brokers or market data sources.
Mixing everything into one service makes deployments risky.
Common split:
You do not get to choose your traffic patterns. The market chooses them for you, so stress testing isn’t optional. Tools like Apache JMeter are often used to simulate peak loads and see where the system bends, or breaks, before real users find out.
Mobile is its own threat model: rooted devices, interception, reverse engineering, and session hijacking. This is where OWASP MASVS helps, because it gives you concrete categories to test against.
Integrations are where timelines slip and incident tickets multiply. Plan them early.
If you connect to one broker, your integration surface is smaller. If you connect to multiple, you’ll usually need an abstraction layer so the rest of your system isn’t tied to one vendor’s quirks. That also makes it easier to support more instrument types without rewriting your trading core every time you add a new brokerage API.
Market data comes with:
Plan for caching and throttling. Also, plan for what happens when data goes stale.
Some teams integrate tools like MetaStock or TradingView for charting and technical analysis, instead of building the entire charting layer from scratch.
News inside a trading app can drive engagement, but it can also drive support load if it’s noisy or irrelevant. That’s why many platforms integrate third-party financial news feeds for in-app updates, then filter and personalize what users see so it stays useful instead of overwhelming.
If you offer guided portfolios, risk profiling, and auto-rebalancing, you’re stepping into suitability and advice territory in many jurisdictions. That changes your compliance posture fast. Many trading platforms handle this by integrating robo-advisory capabilities that build portfolios based on a user’s profile and goals, then keep them on track with periodic rebalancing rules.
Let’s map the work in a way a product lead and a CTO can use.
Let’s be direct: you’re not just buying code, you’re buying execution under pressure.
Here’s the partner checklist that actually matters.
Look for proof of:
If a vendor jumps straight to UI without asking about:
That’s a red flag.
Ask how they handle:
If they don’t talk about load testing tools and scenarios, push back.
A good team will break costs down by:
not by hand-wavy “packages.”
If you’re looking specifically for stock trading app development services, this is the kind of conversation you want in the first week, not after the contract is signed.
If you’re comparing vendors right now and need a sanity check, here’s a simple next step:
Write down your jurisdiction scope, your brokerage approach, and your must-have integrations. Then use that as the baseline to evaluate a stock trading app development company.
Once those three are clear, everything else gets easier. And if you want a partner that has already built a trading mobile app with real-time analytics, portfolio management, broker integrations, and heavy testing under load, Innowise is a strong place to start.

Chief Delivery Officer & Head of Competence Center
Siarhei works at the intersection of tech and business, helping companies build systems that work smarter and solve real operational and strategic challenges. With deep expertise in FinTech and enterprise systems, he’s led projects that connect strategy with execution — from automation and AI deployment to core banking platforms implementation. The goal is always the same: make things work better for the business and the people behind it.










Your message has been sent.
We’ll process your request and contact you back as soon as possible.

By signing up you agree to our Privacy Policy, including the use of cookies and transfer of your personal information.